Trust Computed at the
Moment of Action.
Not a static score. Not a cached permission. Trust is computed in real time from four independent validation layers: cryptographic, behavioral, contextual, and reputation. Every action is assessed before execution proceeds.
Validation Layers
ms ZKP Verification
% System Uptime
Trust Recalculation
Four-Layer Validation
Independent layers. Composite assessment. Deterministic decision.
Each layer operates independently and contributes to a composite risk assessment. The engine evaluates all layers simultaneously and returns a deterministic pass/fail decision bound to the governance zone configuration.
Cryptographic Layer
Ed25519 and CRYSTALS-Dilithium dual signatures provide quantum-resistant verification. Certificate chain validation traverses from leaf to root authority with hardware-backed key storage through TPM and Secure Enclave integration.
Behavioral Layer
LSTM neural network anomaly detection profiles interaction patterns, typing cadence, and session behavior. Continuous drift detection identifies compromised sessions before credential misuse occurs.
Contextual Layer
Geolocation, device fingerprinting, IP reputation, and time-based access patterns contribute to a multi-signal risk assessment evaluated at the moment of every action.
Reputation Layer
Multi-dimensional trust score aggregation from historical interactions, credential provenance, and peer attestations. On-chain behavior scoring derived from wallet and credential history across all Soulverse layers.
Core Components
The components that power real-time trust computation.
The Trust Engine is not a single monolith. It is a composition of purpose-built components from the Soulverse architecture, each handling a specific dimension of trust validation. Together, they produce a single deterministic outcome for every action.
Trust Protocol
The engine's core: combines a Dynamic Trust Score (real-time onchain behavior score from the Soulogram) with a Modular Trust Engine (entity-defined rules that validate execution at runtime). Together they produce a deterministic pass/fail for every action.
Dynamic Trust Score
Computed in real time from behavioral history, credential provenance, and network relationships. The score is a living metric that rises or falls based on the entity's continuous interaction with the infrastructure.
Trust Graph
Maps the relationship topology between entities, credentials, and governance zones. The graph enables transitive trust evaluation, detecting when indirect relationships create authorization paths or risk exposure.
Threshold Governance
Operators define minimum trust scores, required credential sets, and behavioral conditions for each action type. The engine enforces these thresholds deterministically at the moment of execution.
Anomaly Detection
LSTM-based behavioral profiling and multi-signal contextual analysis run continuously. When deviation exceeds configured thresholds, the engine suspends trust score propagation and triggers re-verification.
Continuous Recalculation
Trust is never cached. Every validation request triggers a fresh computation across all four layers. Score decay, credential expiry, and governance state changes are reflected immediately.
Validation Flow
From action request to deterministic decision in five steps.
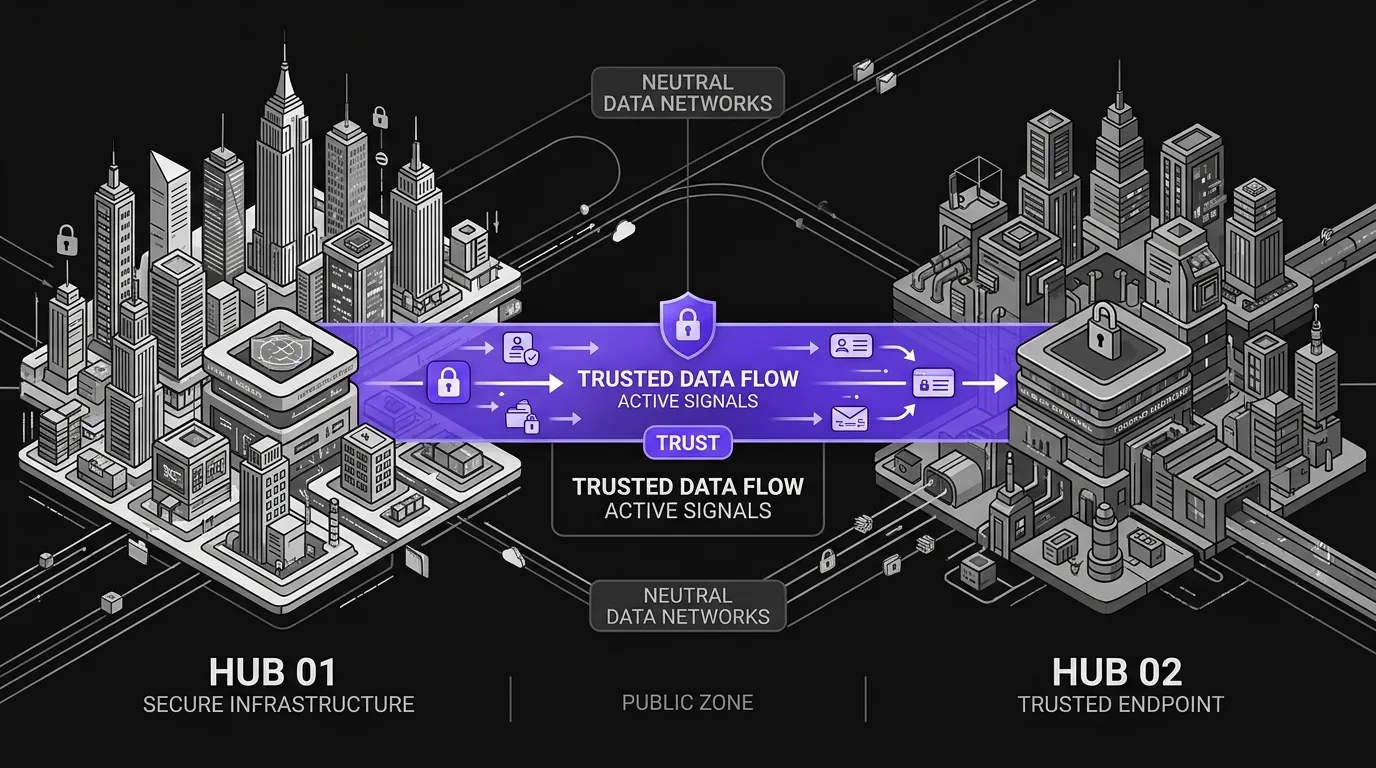
Whether the entity is a financial institution, an industrial controller, or an autonomous AI agent, every trust assessment follows the same four-layer evaluation path.
Action Initiated
An entity (human, institution, machine, or AI agent) initiates an action that requires trust validation. The request includes the entity's DID, relevant credentials, and action context.
Four-Layer Assessment
The Trust Engine evaluates the request simultaneously across cryptographic, behavioral, contextual, and reputation layers. Each layer produces an independent risk signal.
Composite Score Computed
Signals from all four layers are aggregated into a composite trust score. The scoring algorithm weights each layer based on the action type and governance zone configuration.
Threshold Evaluation
The composite score is compared against operator-defined thresholds for the requested action. Governance policies, credential requirements, and delegation constraints are evaluated in parallel.
Deterministic Decision
The engine produces a signed validation assertion: pass or fail. No partial approvals, no deferred decisions. The assertion is passed downstream to settlement and execution layers.
Where Trust Matters
Real-world scenarios where trust is the execution gate.
Financial Services
Cross-Border Payment Authorization
Before any cross-border settlement executes, both counterparties' trust scores are computed in real time. Credential provenance, behavioral signals, and governance zone compliance are validated simultaneously, catching authorization gaps before they become failed settlements.
Engineering & Manufacturing
Safety-Critical Operations
Every operator, machine controller, and safety system carries a live trust score. When an operator initiates a high-risk procedure, the engine validates their certification status, behavioral history, and equipment trust scores before the action proceeds.
AI & Autonomous Systems
Autonomous Agent Governance
AI agents operate within trust score boundaries that constrain their autonomy. As agents accumulate interaction history, their trust scores evolve. Agents that deviate from expected behavior patterns see immediate trust score reduction and scope restriction.
Performance Specifications
Benchmarked, measured, and production-validated.
ZKP Verification
142ms
Average zero-knowledge proof validation latency at 99th percentile across all supported proof systems
DID Resolution
<100ms
Decentralized identifier resolution at 99th percentile across all supported DID methods
System Uptime
99.99%
Four-nines availability with blockchain node redundancy and automatic failover
Transaction Throughput
10,000+ TPS
Peak load capacity across Polygon Layer 2 infrastructure with burst handling
Trust Score Refresh
Real-time
Every validation request triggers fresh computation. No cached scores, no stale assessments
Anomaly Detection
>3σ trigger
Behavioral deviation beyond 3 standard deviations triggers automatic trust suspension
Enterprise Capabilities
Built for institutional deployment at sovereign scale.
The Trust Engine is designed for environments where trust decisions carry regulatory, financial, and safety consequences. Every capability is built for multi-tenant isolation, compliance auditability, and quantum-resistant security.
Policy-Based Authorization
Attribute-based access control with operator-configurable policies. Each governance zone defines its own trust thresholds and required credential sets.
Threshold Permissions
Configurable minimum trust scores per action type. High-value transactions require higher thresholds than read-only operations.
Dispute Resolution
Built-in arbitration framework with multi-party evidence collection. Trust score disputes are resolved through structured protocols.
Quantum-Resistant Cryptography
CRYSTALS-Dilithium post-quantum signatures for long-term security. Hardware-backed key storage with TPM and Secure Enclave integration.
Multi-Tenant Isolation
Namespace management ensures trust computations are isolated between tenants. Cross-tenant trust relationships require explicit governance approval.
Audit Logging
Every trust decision is logged with full provenance. Compliance reporting generates audit trails linking decisions to the signals that produced them.
Continue exploring the architecture.
The Trust Engine builds on verified identity and credentials. See how governance, settlement, and execution consume trust assessments to authorize real-world actions.