Every Action Traces Back
to Delegated Authority.
Not static permissions. Not role-based access. The Authority Layer resolves live delegation chains at the moment of execution, verifying that every entity, from a board resolution to an AI agent, holds an unbroken, unexpired chain of delegated authority for the specific action it is attempting.
Entity Types Authorized
Chain Resolution
Static Permission Lists
Provenance Trail
Authority Domains
One delegation framework for every entity type.
Humans, institutions, AI agents, machines, and IoT devices all operate within the same delegation infrastructure. Authority is not a role assignment. It is a verifiable chain resolved at execution time.
Human Delegation
Board resolutions, signing authority mandates, and operational permissions are expressed as verifiable delegation chains. Each link in the chain carries scope constraints, expiration windows, and revocation hooks verified at the moment of action.
AI Agent Authorization
Autonomous agents carry delegation credentials that trace every action to the human or institutional authority that authorized it. Scope boundaries limit what the agent can do, and delegation depth limits how far authority can cascade.
Institutional Hierarchies
Multi-tier corporate structures express signing authority through hierarchical delegation. A subsidiary can only exercise the scope its parent has delegated, verified in real time against the current organizational graph.
Cross-Institutional Mandates
When counterparties interact across institutional boundaries, delegation chains from both organizations are validated simultaneously. Neither party can exceed the authority scope granted by their respective governance structures.
Machine & IoT Authority
Equipment and industrial controllers carry authority credentials bound to their operational scope. A crane operator credential only authorizes loads within the certified weight range. A sensor can only publish to its authorized data channels.
Emergency & Override Protocols
Time-bound emergency delegations can be issued with elevated scope but automatic expiry. Every override action is logged with full provenance, ensuring auditability even in crisis response scenarios.
Core Components
The components that power real-time authority resolution.
The Authority Layer is not a permissions database. It is a composition of purpose-built components from the Soulverse architecture: delegation registries, scope enforcement, temporal management, chain validation, and audit infrastructure working together modularly to resolve authority at the exact moment of execution.
Delegation Registry
Stores and resolves delegation chains as verifiable credential graphs. Each delegation link contains the delegator DID, delegatee DID, scope constraints, temporal bounds, and revocation conditions. Resolution follows the chain in real time.
Scope Enforcement Engine
Evaluates whether the requested action falls within the delegated scope at the moment of execution. Scope is not a static permission list. It is a set of constraints evaluated against the current policy state, credential status, and governance zone.
Temporal Authority Manager
Manages time-bound delegations with automatic expiry, scheduled activation, and renewal workflows. Authority that was valid yesterday may not be valid today. Every timestamp is evaluated at execution time, not at issuance.
Chain Integrity Validator
Walks the complete delegation chain from the acting entity to the root authority, verifying each link has not been revoked, each scope has not been narrowed, and each temporal window remains active. A single broken link halts execution.
Authority Resolution Service
Resolves "who authorized this action" queries across institutional, jurisdictional, and operational boundaries. Produces a verifiable provenance trail from the executing entity through every delegation link to the root authorizing body.
Delegation Audit Log
Every delegation issuance, scope modification, and revocation event is recorded with cryptographic provenance. Auditors can reconstruct the complete authority state at any historical point in time for compliance and forensic purposes.
Authority Resolution Flow
From action request to authority assertion in five deterministic steps.
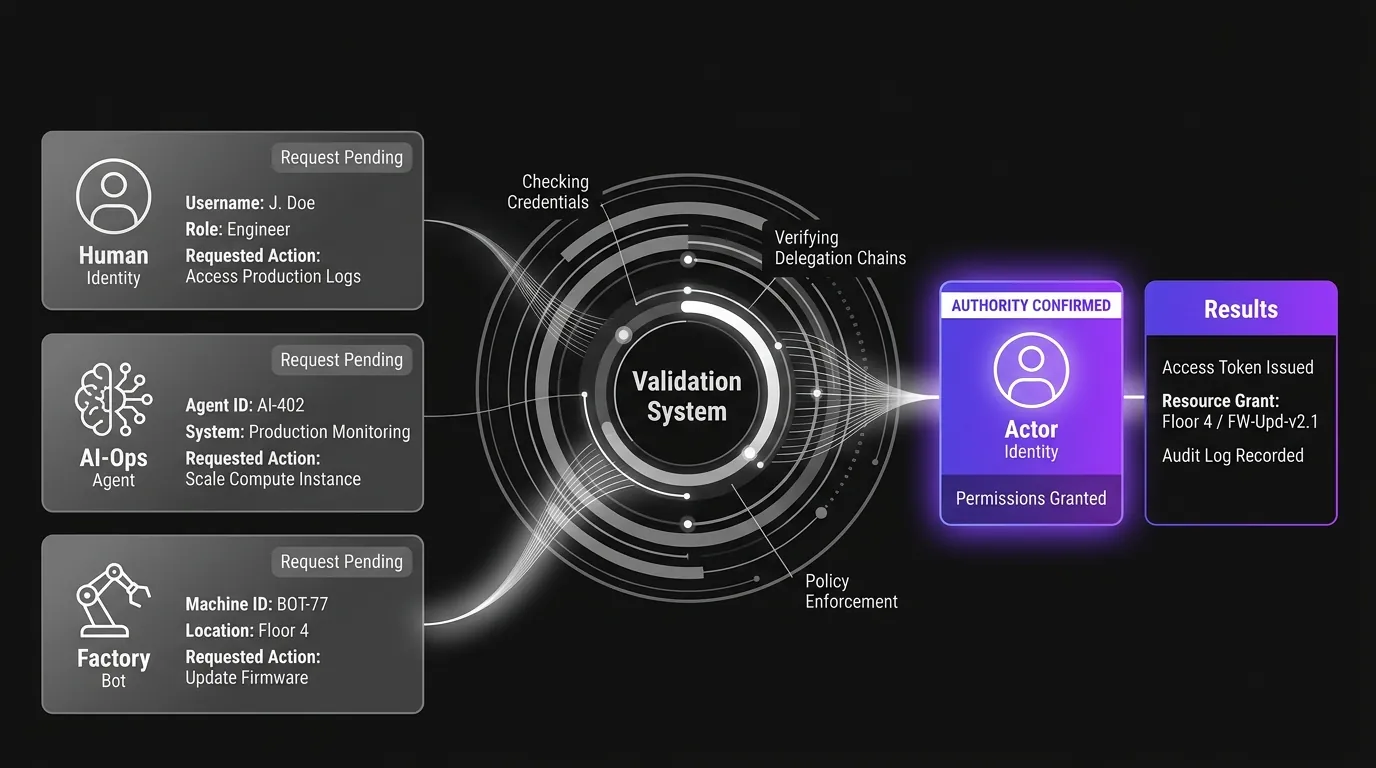
Whether the entity is a human operator, an AI agent, or a machine controller, every authority check follows the same delegation chain resolution path.
Action Initiated by Entity
An entity (human, AI agent, machine, or institutional service) initiates an action that requires authorization. The request carries the entity's DID and the delegation credential chain it claims authorizes the action.
Delegation Chain Resolved
The Authority Resolution Service walks the delegation chain from the acting entity through each intermediate delegator to the root authority. Every link is resolved against the current state of the Delegation Registry.
Scope Constraints Evaluated
The Scope Enforcement Engine verifies that the requested action falls within the intersection of all scope constraints along the delegation chain. Authority narrows at each level: a delegatee can never exceed their delegator's scope.
Temporal Windows Verified
The Temporal Authority Manager confirms every delegation in the chain is currently active. Not yet activated, expired, or suspended delegations break the chain and halt execution immediately.
Authority Assertion Issued
A signed authority assertion is produced: authorized or unauthorized. The assertion includes the full chain provenance, scope evaluation results, and temporal verification outcomes for downstream consumption by the Execution Layer.
Modular Architecture
How the Authority Layer connects to every other layer.
Authority does not operate in isolation. It consumes identity proofs, credential verifications, trust signals, and governance policies from the other layers of the Soulverse architecture. This modular composition is the architectural strength: each layer does one thing well, and the Authority Layer orchestrates them into a unified authorization decision.
Identity Layer
Every entity in the delegation chain is authenticated through its DID before authority resolution begins. The Identity Layer confirms the acting entity is who it claims to be.
Integration Point
The Authority Layer consumes identity proofs as the first checkpoint. No delegation chain is walked until the acting entity is cryptographically authenticated.
Credential Layer
Delegation credentials are issued, stored, and verified through the Credential Layer infrastructure. Revocation registries, schema validation, and selective disclosure all apply to delegation credentials.
Integration Point
Delegation chains are expressed as verifiable credentials. The Authority Layer uses the Credential Layer's verification engine to validate each link.
Trust Graph
Dynamic trust scores influence authority thresholds. An entity with a declining trust score may see its effective authority scope narrowed in real time, even if the delegation credential remains technically valid.
Integration Point
The Trust Graph provides real-time behavioral signals that modulate authority enforcement. High-risk actions require higher trust thresholds.
Governance Layer
Governance zones define the policy context for authority evaluation. A delegation valid in one governance zone may be insufficient in another. Cross-jurisdictional authority mapping runs through the Governance Layer.
Integration Point
The Governance Layer sets the rules the Authority Layer enforces. Policy zones determine required delegation depth, scope requirements, and temporal constraints.
Where Authority Matters
Real-world scenarios where delegation chain verification prevents unauthorized execution.
Financial Services
Multi-Level Treasury Authorization
A payment above the threshold requires authorization from the treasury desk, approved by the CFO, whose signing authority was delegated by the board. The Authority Layer walks this chain in real time and verifies every link before settlement executes.
Technology & Automation
Autonomous Agent Task Boundaries
An AI agent tasked with portfolio rebalancing carries a delegation credential from its operator, who received delegation from the fund manager. The agent can only execute trades within the scope its operator was granted, which is itself bounded by the fund mandate.
Engineering & Industrial
Cross-Border Equipment Operation
A crane operator certified in Jurisdiction A deploys to Jurisdiction B. The Authority Layer verifies the operator's certification delegation chain, maps it through the cross-jurisdictional governance zone, and confirms the delegation scope covers the specific equipment class.
Continue exploring the architecture.
The Authority Layer builds on identity, credentials, trust, and governance. See how delegation chain verification connects to the other layers of the Soulverse infrastructure.