Industry Solutions
Industrial & Engineering
Unified identity for IoT devices, supply chains, and field operations
Engineering operations manage billions of IoT devices across manufacturing, mining, utilities, and transportation with no unified identity framework. Soulverse provides the identity layer that binds devices, technicians, and components to verifiable credentials and governance state.
The Problem
Critical gaps in current operations.
IoT Device Identity Crisis
Billions of connected devices across 30+ platforms lack standardized authentication. No unified framework for device lifecycle management, provenance, or decommissioning.
Supply Chain Verification Gaps
Multi-tier engineering supply chains lack cryptographic proof of supplier certifications. Manual verification of component authenticity creates counterfeit risk.
Field Service Security
20,000+ field technicians require secure authentication. Username/password systems are vulnerable to phishing, and biometric data storage raises privacy concerns.
Digital Twin Provenance
Virtual replicas of physical assets lack verifiable links to real-world identity. No cryptographic proof that simulation data corresponds to actual device state.
Soulverse Solution
How Soulverse addresses each gap.
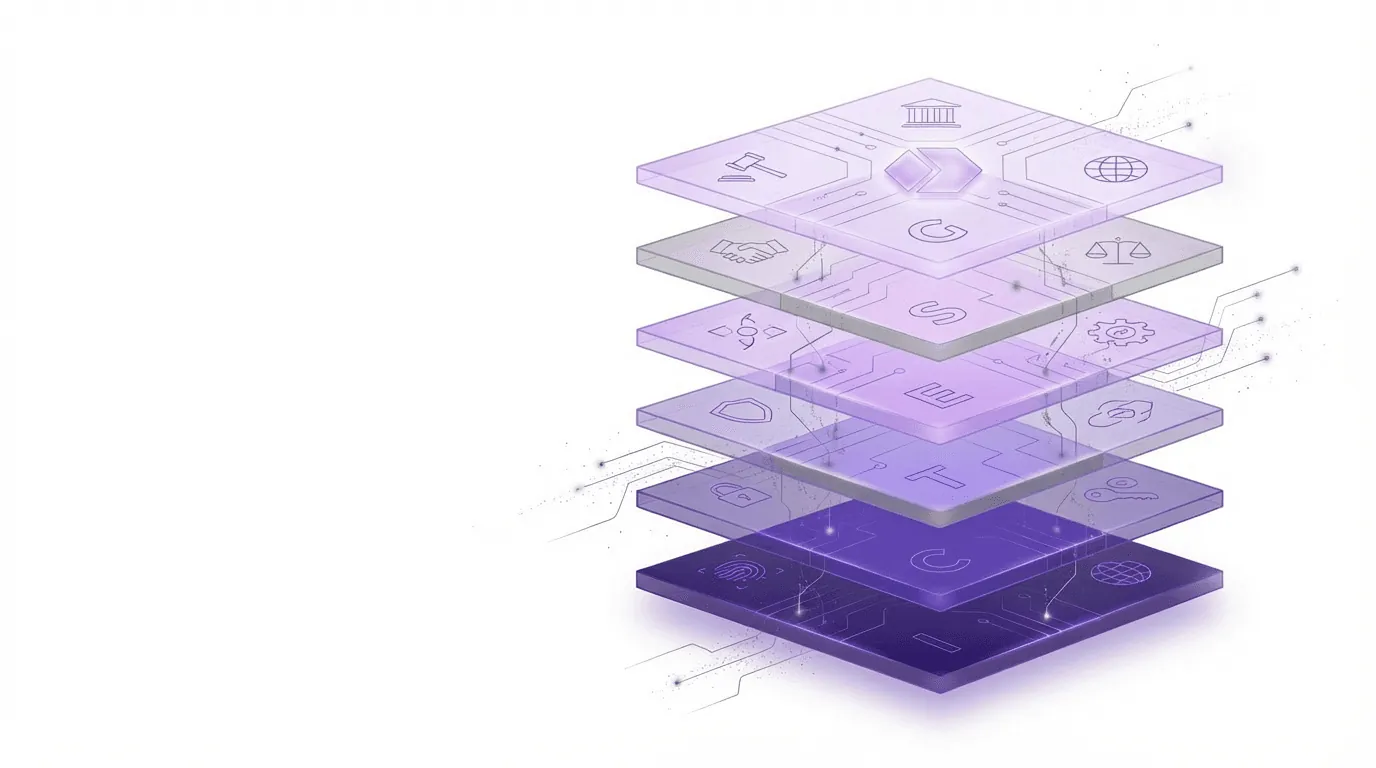
Each use case maps directly to the six-layer architecture, activated through operator roles specific to your industry.
Secure IoT Device Identity
Every IoT device (sensor, actuator, smart meter, vehicle ECU) receives a unique Soul ID with hardware-backed key storage. Device-to-device and device-to-cloud authentication uses DID-based certificates.
Outcomes
Verifiable Supply Chain
Every supplier receives a Soul ID. ISO 9001, AS9100, and IATF 16949 certifications are issued as Soulogram credentials. Components are serialized with DIDs linking to manufacturing VCs.
Outcomes
Field Technician Authentication
Field technicians authenticate using FIDO2-compliant biometrics linked to Soul ID. ZKP enables proving certifications without revealing personal details. Offline verification supports remote operations.
Outcomes
Digital Twin Provenance
Digital twin solutions gain verifiable provenance through Soulogram credentials that cryptographically bind simulation data to real-world device identity and state.
Outcomes
Measurable Impact
Operational outcomes from deployment.
Reduction in Onboarding Cost
Device onboarding cost drops from $50 to $5 per device through zero-touch provisioning.
Fewer Security Incidents
Unified device identity framework eliminates spoofing and man-in-the-middle attack vectors.
Device Authentication
Down from 2-5 seconds, a 90% reduction in device authentication latency.
Faster Cross-Platform Coordination
Single validation checkpoint replaces sequential multi-system approval chains.
Based on architectural modeling and industry benchmark analysis.
Architecture Mapping
How the six-layer architecture maps to industrial & engineering.
Standards Alignment
Compliance frameworks addressed.
Ready to discuss your deployment?
Whether you are evaluating the architecture, planning a pilot, or scoping enterprise integration, start the conversation.